Posted by
1
comments (0)
Last week, I was the victim of an Email Hacker. For the first time in 12 years of having my Yahoo email, someone managed to get in and change my email password. As I tried frantically for days to get control of my account back, I realized that I had made several small mistakes that - if I had known better - could have prevented the nightmare it quickly became. You see, not only do I have a Yahoo email account, but I also have Yahoo Messenger, a Yahoo Website, a secondary Yahoo email, the customized Yahoo Page, but I am also on many Yahoo groups. And while I LOVE Yahoo because everything can be accessed via one email and one password, you can imagine how frantic I was to suddenly not be able to contact anyone I know and tell them what happened. Here's what I learned, and what you should consider when thinking about your own email account, messenger account, and social networking sites:
- 1. Get a secondary email account with another email provider. This was the first lesson I immediately learned. You see, when I got locked out of my account, I immediately tried to change the password via the "Forgot Your Password?" link that every email account offers. The only problem was - my secondary email account was the email account linked to my main account. That means, I was locked out of both accounts and could not "click on the link" that Yahoo would send to my secondary email account for identity verification. For the first time, I realized how stupid I had been to not link this account to an outside email, but like I've already said, this was the first time this has ever happened to me - ever. Needless to say, I now have a gmail account as well, even though I will probably never use it.
- 2. Upload your contact list to your secondary account. The second thing I realized after being locked out of my email account was that I was locked out of my contact list. While I still had phone numbers of all the most important people in my life, there were a lot of emails I wanted and needed. Even worse, what if the hacker was spamming all my friends or colleagues. What if I was about to lose valuable networking contacts because of this? Thankfully, my iPod Touch had uploaded all of those contacts the first time I had set it up, but it took a couple days of email silence before I remembered that I had that backup list at all. I was saved by an amazing little electronic, but considering how irritating it is to send a message on such a small screen, I've definitely transferred my email to my secondary email account.
- 3. Never have one of your security questions be, "What is my favorite...?" This was my third mistake. Yahoo let me pick my own email security questions, and the question I chose was, "Who is my favorite author?" as my security question. While this would seem like a very personal and reasonable question to pick, I chose the question more than a year ago. Suddenly, I couldn't remember who my favorite author had been last year. I typed in the name of every author I would have possibly answered, and they all came back with a big fat "Try again." Needless to say, the first thing I did when I got in was change the security question to something that doesn't change...like "what is your second child's middle name?" or "what was the name of your childhood pet?" Those kinds of questions have consistent answers year after year.
- 4. Never have your password related to something that can be found at a social networking site. After many, many failed attempts - I mean, I was even purposefully spelling names wrong just in case I spelled them wrong a year ago - I thought to myself, "Who was my favorite author a year ago - when I set up the question?" I remembered that I had put my favorite books in my social networking site profiles at various periods of my life. So I checked Facebook and MySpace, and sure enough, there were my favorite books listed on both sites for the different years that I opened or updated those accounts. Then I realized, I generally use the same ID on all sites - after all, my profile ID is my brand - thus, it would be easy for a hacker to find those answers, especially a "Friend." That may be how my hacker got in, because they found the answers at my networking sites. So, when choosing a security question, don't pick something that can be found through those sites. So, questions like, "what city was your father born in?" or "where did you graduate high school?" would be bad questions to ask. After all, your father is probably your friend on Facebook / MySpace, and you've probably listed your graduation year and high school on a site like Classmates.com - I mean seriously, who doesn't want to be contacted by old high school friends?
- 5. Convert your private contact information into codes. One of the scariest things for me on the financial side was the realization that I keep a lot of login and passwords in my private email contact list. I find it useful because it can be accessed from anywhere, and it's harder to lose this way. (I used to keep it in my contact list on my phone, but when you lose your phone a few times, you quickly realize what a bad idea that is.) I still maintain that this is a good way to keep logins and passwords, but I acknowledge that maybe those passwords and logins should be dummies in case this happens to you. Thus, instead of listing a password as "tunafish" for an example, you could say, "The food I hate the most" or "Marine Biology" as a hint. That leaves a lot of answers that most people won't guess at, and it allows you to just glance at and go "Oh yeah!"
- 6. You CAN lock your account from outside the account. This was a blessing in disguise. When I failed to get into my account, I was able to lock it from the outside for a 24-hour period. Yahoo offered this as a manual selection, but for many accounts, when you enter the wrong password 5 times, that account will automatically lock. I locked my account and came back every day and re-locked it until I was able to talk to customer service on the phone. By doing this, the hacker only had enough time to hack one personal account from my emails and contacts before they were kicked out. Thus, when I got my email access back and saw the "confirmation" email that Upromise had sent me, I was able to quickly head over there and change all of my security information, passwords, and notify their customer service department before my kids' college funds were drained.
- 7. Immediately begin changing all of your passwords on all of your private accounts. As a bookkeeper who deals with fraud a lot, the very first thing I did was head over to all of my accounts that had money balances and change the passwords and security questions - after locking the account, of course. Thus, the hacker was only able to get into one account, and that was the one account I forgot about. So, if this happens to you, be smart and head immediately to your bank and credit card websites and change those passwords. That way, you can head a thief off at the pass.
Posted by
1
comments (0)
Eric Larkin in PC World reports that we need to get rid of myths about the internet in order to stay safe online.
Myth #1:
Maladjusted teens vandalize your computer.
Reality #1:
Gone are the days when teenagers looked for 15 minutes of fame. Organized crime is the culprit. They want money. Online black marketers place malware on computers to make money. They take over PCs to send spam, steal logins and credit card information, or hack game accounts. They use stolen webmail accounts to request transfers from contact lists and raid online games to sell the items or the in-game currency for real money. Financial fraud by cyber-criminals have cost consumers and businesses billions of dollars.
Myth #2:
All you need is a good antivirus program.
Reality #2:
Wrong. A good antivirus program will help a good deal, but antivirus companies are locked in a constant battle with cyber-criminals who make every effort to stay one step ahead of antivirus software. Yes, many times the security software can prevent the attacks, but other times there are holes in the software and the criminals get the upper hand. You need more security software than just a good antivirus program to protect you from cyber-crime.
Myth #3:
You're fine if you are just careful where you surf.
Reality #3:
This way of thinking is outdated. Years ago you could tell if a site was dangerous just by looking at it, and if you were careful with your emails, you could go without antivirus software. Not anymore. Now personal pages and big-name company sites are hacked by cybercriminals using flaws in the security software to install malware. You would have to be an expert to recognize a hacked page or an email that was attacked. Besides antivirus software, you need antispyware, antirootkit, and a bidirectional firewall along with a team of techs to protect you from cyber-criminals.
Myth #4:
"If it ain't broke don't fix it" requires knowing when something is broken.
Reality #4:
These days there are malicious hidden processes, threats, files, or registry keys and you need advanced anti-rootkit technology to remove them.
Myth #5:
The worse myth. We're all doomed. Stay offline.
Reality #5:
Yes, you can get hacked, but if you know the risks and prepare adequately you can enjoy what the Web has to offer. By following these simple steps, you can be protected from cybercriminals.
* Install antivirus+antispyware, antirootkit, and a bidirectional firewall onto your computer.
* Make sure your computer has daily security updates, automatic upgrades to new software, and full security software support.
* Have your computer monitored daily for malware and have malicious codes stopped before they can harm your computer.
* Get protection for emails and attachments.
* Have your own team of techs to keep your computer clean and running well.
Don't fall hostage to cybercriminals. Don't accept the worst myth that the crooks own the internet and that the only good option is to use the internet as little as possible.
Log onto my informational blog http://www.crimeandjustice4all.com to learn about a Managed Internet Security Service and how it can protect you, your family, and your business from cybercrime. I am Miriam Bobroff, President and CEO of Bubby's Business, Inc. an international marketing and distribution company that offers education and cutting edge solutions to the problem of Cybercrime. I have always helped people to improve the quality of their lives and I now include a Managed Internet Security Service into my business that helps people fight the war on Cybercrime and keeps them safe and secure from cybercriminals.
For more information, log onto http://www.crimeandjustice4all.com or you can reach me at 888-809-3798 or email me at crimeandjustice4all@gmail.com.
Myth #1:
Maladjusted teens vandalize your computer.
Reality #1:
Gone are the days when teenagers looked for 15 minutes of fame. Organized crime is the culprit. They want money. Online black marketers place malware on computers to make money. They take over PCs to send spam, steal logins and credit card information, or hack game accounts. They use stolen webmail accounts to request transfers from contact lists and raid online games to sell the items or the in-game currency for real money. Financial fraud by cyber-criminals have cost consumers and businesses billions of dollars.
Myth #2:
All you need is a good antivirus program.
Reality #2:
Wrong. A good antivirus program will help a good deal, but antivirus companies are locked in a constant battle with cyber-criminals who make every effort to stay one step ahead of antivirus software. Yes, many times the security software can prevent the attacks, but other times there are holes in the software and the criminals get the upper hand. You need more security software than just a good antivirus program to protect you from cyber-crime.
Myth #3:
You're fine if you are just careful where you surf.
Reality #3:
This way of thinking is outdated. Years ago you could tell if a site was dangerous just by looking at it, and if you were careful with your emails, you could go without antivirus software. Not anymore. Now personal pages and big-name company sites are hacked by cybercriminals using flaws in the security software to install malware. You would have to be an expert to recognize a hacked page or an email that was attacked. Besides antivirus software, you need antispyware, antirootkit, and a bidirectional firewall along with a team of techs to protect you from cyber-criminals.
Myth #4:
"If it ain't broke don't fix it" requires knowing when something is broken.
Reality #4:
These days there are malicious hidden processes, threats, files, or registry keys and you need advanced anti-rootkit technology to remove them.
Myth #5:
The worse myth. We're all doomed. Stay offline.
Reality #5:
Yes, you can get hacked, but if you know the risks and prepare adequately you can enjoy what the Web has to offer. By following these simple steps, you can be protected from cybercriminals.
* Install antivirus+antispyware, antirootkit, and a bidirectional firewall onto your computer.
* Make sure your computer has daily security updates, automatic upgrades to new software, and full security software support.
* Have your computer monitored daily for malware and have malicious codes stopped before they can harm your computer.
* Get protection for emails and attachments.
* Have your own team of techs to keep your computer clean and running well.
Don't fall hostage to cybercriminals. Don't accept the worst myth that the crooks own the internet and that the only good option is to use the internet as little as possible.
Log onto my informational blog http://www.crimeandjustice4all.com to learn about a Managed Internet Security Service and how it can protect you, your family, and your business from cybercrime. I am Miriam Bobroff, President and CEO of Bubby's Business, Inc. an international marketing and distribution company that offers education and cutting edge solutions to the problem of Cybercrime. I have always helped people to improve the quality of their lives and I now include a Managed Internet Security Service into my business that helps people fight the war on Cybercrime and keeps them safe and secure from cybercriminals.
For more information, log onto http://www.crimeandjustice4all.com or you can reach me at 888-809-3798 or email me at crimeandjustice4all@gmail.com.
Posted by
1
comments (0)
With the growing popularity of the Internet more and more people are communicating via email. This fast and efficient method of communication is perhaps the preferred method of online communication at the present with thousands upon thousands of emails being sent each day. The many uses of email are what make it so appealing and so versatile. Whether you are sending a greeting to a grandparent or sending files to a coworker, you can easily utilize email to do so.
Email has come quite a long way since its introduction, yet it is still used for many of the same reasons. Basic electronic communication has essentially evolved into a more resourceful tool as one has the ability to do much more now then they once could. Along with the usual sending of files and text messages through email, one can send greeting cards, manage their emails by assigning them to folders or classifying them as junk and even organize and manage their daily tasks on some email servers.
This wonderful tool is not without its downside however. Some people choose to send worms and viruses via email and in the process infect and damage quite a lot of computers. A virus email can often be very difficult to detect, especially to someone with very little knowledge of computer viruses and how they work. If you notice that you have an anonymous email or an email with a name foreign to you then you may not want to open this email as may likely be a viruses and the mere act of opening the email makes your computer susceptible to infection.
Along with the abovementioned problems privacy has also become an issue with email activity. Virtually every email that you send has to go through a number of computers before it reaches the inbox of the intended receiver and along the way there exists a distinct possibility that an individual could hack into your email and read it. Thus it is imperative that you have a bullet proof password.
Email has come quite a long way since its introduction, yet it is still used for many of the same reasons. Basic electronic communication has essentially evolved into a more resourceful tool as one has the ability to do much more now then they once could. Along with the usual sending of files and text messages through email, one can send greeting cards, manage their emails by assigning them to folders or classifying them as junk and even organize and manage their daily tasks on some email servers.
This wonderful tool is not without its downside however. Some people choose to send worms and viruses via email and in the process infect and damage quite a lot of computers. A virus email can often be very difficult to detect, especially to someone with very little knowledge of computer viruses and how they work. If you notice that you have an anonymous email or an email with a name foreign to you then you may not want to open this email as may likely be a viruses and the mere act of opening the email makes your computer susceptible to infection.
Along with the abovementioned problems privacy has also become an issue with email activity. Virtually every email that you send has to go through a number of computers before it reaches the inbox of the intended receiver and along the way there exists a distinct possibility that an individual could hack into your email and read it. Thus it is imperative that you have a bullet proof password.
Posted by
1
comments (0)
Grocery coupons are a great way to save money when you go grocery shopping. With the economy in a rut, more and more people are looking for creative ways to make their budget last longer and make their spending more cost efficient. You can either put the money you save into a savings account and keep them for a rainy day, or use them for other financial needs. Research estimates that there are billions of dollars worth of coupons out there - more or less about $360 billion - so you can definitely save a lot of money when you collect, compile, and use these coupons. Furthermore, restaurant coupons such as pizza hut coupons can save you you money while you dine out.
Some might say that the rewards to using grocery coupons are small, but they are mistaken. Looking at things in the short view, this might be true, but the more important thing is the effects in the long run, and as long as you use your coupons as well as your resources wisely, the rewards can be considered to be more than enough. Coupons for groceries are a good way of saving money if you use them properly.
However, in one relatively new trend that's starting to pop up, namely printable grocery coupons, there can be certain disadvantages to using these types of coupons. Printable grocery coupons are basically grocery coupons to print from different websites that offer grocery deals and promotions. You go to a site, and maybe register and fill out a short form, and then you get grocery coupons to print out and use in your grocery shopping.
One disadvantage is that promotions on the internet are loosely regulated, which is why there a lot of scams and false claims out there. So you need to be careful so that your effort will not be wasted. Sometimes scammers use the information you give out to hack emails and steal your identity. So always be careful of the offers you take and the so-called promotions you download.
Another disadvantage is that the coupons you print out may not be honored by the local grocery store you are going to. This is because that since printable grocery coupons are easily altered digitally - which is called coupon fraud - some grocery stores avoid getting scammed by these fake coupons by opting not to honor online print out coupons. So make sure that your grocery honors them before starting to collect these kinds of coupons. Same goes for the restaurant coupons.
The advantage with online coupons though, is that you will be able to find these very easily - a simple search on Google or Yahoo or the like will yield you dozens of different coupons, offers and promotions you can use to stretch your grocery budget further. Online coupons are also easier to collect, as everything is on the web, and you do not need to scrounge and browse so many different magazines and publications and cut out these coupons to be able to avail of them. With online print outs, you merely need to print them out and you have your coupons instantly.
Online coupons are very convenient to find and use, just make sure that you weigh all the pros and cons before deciding to use them.
Some might say that the rewards to using grocery coupons are small, but they are mistaken. Looking at things in the short view, this might be true, but the more important thing is the effects in the long run, and as long as you use your coupons as well as your resources wisely, the rewards can be considered to be more than enough. Coupons for groceries are a good way of saving money if you use them properly.
However, in one relatively new trend that's starting to pop up, namely printable grocery coupons, there can be certain disadvantages to using these types of coupons. Printable grocery coupons are basically grocery coupons to print from different websites that offer grocery deals and promotions. You go to a site, and maybe register and fill out a short form, and then you get grocery coupons to print out and use in your grocery shopping.
One disadvantage is that promotions on the internet are loosely regulated, which is why there a lot of scams and false claims out there. So you need to be careful so that your effort will not be wasted. Sometimes scammers use the information you give out to hack emails and steal your identity. So always be careful of the offers you take and the so-called promotions you download.
Another disadvantage is that the coupons you print out may not be honored by the local grocery store you are going to. This is because that since printable grocery coupons are easily altered digitally - which is called coupon fraud - some grocery stores avoid getting scammed by these fake coupons by opting not to honor online print out coupons. So make sure that your grocery honors them before starting to collect these kinds of coupons. Same goes for the restaurant coupons.
The advantage with online coupons though, is that you will be able to find these very easily - a simple search on Google or Yahoo or the like will yield you dozens of different coupons, offers and promotions you can use to stretch your grocery budget further. Online coupons are also easier to collect, as everything is on the web, and you do not need to scrounge and browse so many different magazines and publications and cut out these coupons to be able to avail of them. With online print outs, you merely need to print them out and you have your coupons instantly.
Online coupons are very convenient to find and use, just make sure that you weigh all the pros and cons before deciding to use them.
Posted by
1
comments (0)
Most of we Internet business folks like losing money on the Internet. If we didn't lose money all the time, we would be out of business. Yes, over ninety percent of we Internet business folk--lose money. It's just part of our business and we can't expect others-- like our wives--to understand that.
Oh, some take the fun out of Internet business by actually making money. These effete snobs are called gurus. I know all of the gurus (well, not personally) and they all know me. They have MY money.
I'm what they call a sucker. P.T. Barnum said that there is a sucker born every minute. I'm sure he was and still is right on that point.
Being an educator, I must make sure all of my readers know what I mean by "effete snob" rather than just "snob." Effete means that the guru works in pajamas, if he works at all, and could care less about you or me as long as we stay on his mailing list. The guru's mailing list is his gold mine.
I'm not an Internet guru so if you do what I do you will keep losing money for sure. I do whatever the gurus tell me.
Yes, the Internet gurus teach the rest of us how to get rich by having an Internet business. In fact, other than porn, teaching folks how to make money on the Internet is the way to make money on the Internet. Here is what I have learned from the gurus:
Don't Quit Your Day Job
Yes, after the guru tells you that you will be living on your own island with your yacht as long as a football field in the harbor and an Lamborghini and a BMW in the garage, they say: DON'T QUIT YOUR DAY JOB!
The gurus give good advice and this is particularly good advice. However, I didn't have a day job to quit so I ignored it and that is probably exactly why I'm not making much money to speak of on the internet to this day.
Get Rich Selling My Product
That's right. The guru will tell you that you can get in business in a few minutes selling his product. This is called the guru's affiliate program. He may call you a partner or associate but its all the same. It cost you nothing to join an affiliate program because, in my experience, that is about what it is worth. Let's say the guru signs up 10,000 affiliates. He now has a mailing list of 10,000 folks he can sell to.
Also, let's say that the guru is selling a product worth $97.00. He pays a commission of $48.50. If his 10,000 affiliates sell 1500 folks his program, they will receive $72,750.00 to split between them. Using the 90% loser rule, $65,475.00 will be split between 1000 affiliates for an average of $654.75. The other 9000 affiliates will average about 81¢.
The above analysis sounds exactly right to me. I think that is about what I average--81¢.
Now, it is not over. The guru receives the same amount of money as his affiliates. If he is selling an ebook that is downloaded, it is all gravy. Yes, he gets $72,750.00! But that is not all. He has added another 1500 names on his mailing list and some of those will become affiliates AND CUSTOMERS.
Now what else does he sell these folks? Well, it goes like this for some gurus. You will remember that he is selling the "How To Get Rich on the Internet" message. If you do as you are told and do as he does, that is, you copy the guru, you will need the stuff to do that. Here's a partial list:
● Web site design program
● Web hosting account
● Mail handling program
● Affiliate program software
● Personal consulting
● BMW
● Lamborghini
● Yacht
There is no end to the products that he will try to sell to his mailing list, not only his own products but also the products of other gurus. He gets first choice on new products and immediately emails his list.
When a guru reports on his web site, "I earned $36,785.42 in only 36 hours," he means it. He just sent a new product sales pitch to his mailing list.
In the mean time, you are trying to sell his product too. You put up an ad using Google AdWords and lo and be hold you learn that your main competitor is guess who? Your guru! He can afford more advertising cost than you can because he makes twice as much as you do on each sale.
The Guru always wins!
You can win too but it will cost you money. You must put up the investment to become a guru.
Develop Products for a Niche Market
This is good advice and the gurus know what they are talking about. That is how some of them got started. Cory Rudl was a guru of gurus. Corey Died in May of 2005 while racing his Porsche (as passenger, not driver). That was a sad day for those of us in "the business." It was especially traumatic for his new bride, God bless her.
Cory started his Internet business in Canada and he sold an ebook on buying cars and parts for certain desirable automobiles.
Cars were his passion. But he soon leaned that he could make more money selling his knowledge of Internet Marketing.
He sold some of the products I mentioned above.
(His company is the Internet Marketing Center which is now operated by another guru named Derek Gehl. It is fortunate that a qualified person like Derek was able to continue the operations. I'm an affiliate signed up by Corey Rudl. I know Derek loves me because he writes to me almost every day. I'm on the list!
Look at the sales letter at http://tinyurl.com/yudz6g to see how this gurus operates.)
I have been involved in two niche market Internet businesses. The first, my son's, is successful: http://www.irishflutestore.com The second is too early to tell but I think it may be a flop if I don't design and produce an additional product. I'm giving away a free .pdf file but it may be the only thing that people need to solve their problem. They are not buying the product. I've hit the market by telling all of my industry work associates and associations worldwide about it and by using AdWords--but no sales. The site is http://www.ceramicdefects.com
The gurus say to expect failures. You have to keep trying new things and evaluating the performance by testing, testing, testing. Traffic is a problem. I have successfully sold money-making-books by advertising my web site (http://www.money-making-books.com) in national magazines. However, the profit margin was too low to warrant my continued efforts. You need to write your own books or ebooks to make it big!
Well, I've got to get out of here. I've got some more testing to do.
The End
John T. Jones, Ph.D. (tjbooks@hotmail.com), a retired college professor and business executive, Former editor of an international engineering magazine. To learn more about Wealthy Affiliate University go to his info site. If you desire a flagpole to Fly Old Glory, go to the business site.
More info: http://www.InternetBusinessToolCenter.com
Oh, some take the fun out of Internet business by actually making money. These effete snobs are called gurus. I know all of the gurus (well, not personally) and they all know me. They have MY money.
I'm what they call a sucker. P.T. Barnum said that there is a sucker born every minute. I'm sure he was and still is right on that point.
Being an educator, I must make sure all of my readers know what I mean by "effete snob" rather than just "snob." Effete means that the guru works in pajamas, if he works at all, and could care less about you or me as long as we stay on his mailing list. The guru's mailing list is his gold mine.
I'm not an Internet guru so if you do what I do you will keep losing money for sure. I do whatever the gurus tell me.
Yes, the Internet gurus teach the rest of us how to get rich by having an Internet business. In fact, other than porn, teaching folks how to make money on the Internet is the way to make money on the Internet. Here is what I have learned from the gurus:
Don't Quit Your Day Job
Yes, after the guru tells you that you will be living on your own island with your yacht as long as a football field in the harbor and an Lamborghini and a BMW in the garage, they say: DON'T QUIT YOUR DAY JOB!
The gurus give good advice and this is particularly good advice. However, I didn't have a day job to quit so I ignored it and that is probably exactly why I'm not making much money to speak of on the internet to this day.
Get Rich Selling My Product
That's right. The guru will tell you that you can get in business in a few minutes selling his product. This is called the guru's affiliate program. He may call you a partner or associate but its all the same. It cost you nothing to join an affiliate program because, in my experience, that is about what it is worth. Let's say the guru signs up 10,000 affiliates. He now has a mailing list of 10,000 folks he can sell to.
Also, let's say that the guru is selling a product worth $97.00. He pays a commission of $48.50. If his 10,000 affiliates sell 1500 folks his program, they will receive $72,750.00 to split between them. Using the 90% loser rule, $65,475.00 will be split between 1000 affiliates for an average of $654.75. The other 9000 affiliates will average about 81¢.
The above analysis sounds exactly right to me. I think that is about what I average--81¢.
Now, it is not over. The guru receives the same amount of money as his affiliates. If he is selling an ebook that is downloaded, it is all gravy. Yes, he gets $72,750.00! But that is not all. He has added another 1500 names on his mailing list and some of those will become affiliates AND CUSTOMERS.
Now what else does he sell these folks? Well, it goes like this for some gurus. You will remember that he is selling the "How To Get Rich on the Internet" message. If you do as you are told and do as he does, that is, you copy the guru, you will need the stuff to do that. Here's a partial list:
● Web site design program
● Web hosting account
● Mail handling program
● Affiliate program software
● Personal consulting
● BMW
● Lamborghini
● Yacht
There is no end to the products that he will try to sell to his mailing list, not only his own products but also the products of other gurus. He gets first choice on new products and immediately emails his list.
When a guru reports on his web site, "I earned $36,785.42 in only 36 hours," he means it. He just sent a new product sales pitch to his mailing list.
In the mean time, you are trying to sell his product too. You put up an ad using Google AdWords and lo and be hold you learn that your main competitor is guess who? Your guru! He can afford more advertising cost than you can because he makes twice as much as you do on each sale.
The Guru always wins!
You can win too but it will cost you money. You must put up the investment to become a guru.
Develop Products for a Niche Market
This is good advice and the gurus know what they are talking about. That is how some of them got started. Cory Rudl was a guru of gurus. Corey Died in May of 2005 while racing his Porsche (as passenger, not driver). That was a sad day for those of us in "the business." It was especially traumatic for his new bride, God bless her.
Cory started his Internet business in Canada and he sold an ebook on buying cars and parts for certain desirable automobiles.
Cars were his passion. But he soon leaned that he could make more money selling his knowledge of Internet Marketing.
He sold some of the products I mentioned above.
(His company is the Internet Marketing Center which is now operated by another guru named Derek Gehl. It is fortunate that a qualified person like Derek was able to continue the operations. I'm an affiliate signed up by Corey Rudl. I know Derek loves me because he writes to me almost every day. I'm on the list!
Look at the sales letter at http://tinyurl.com/yudz6g to see how this gurus operates.)
I have been involved in two niche market Internet businesses. The first, my son's, is successful: http://www.irishflutestore.com The second is too early to tell but I think it may be a flop if I don't design and produce an additional product. I'm giving away a free .pdf file but it may be the only thing that people need to solve their problem. They are not buying the product. I've hit the market by telling all of my industry work associates and associations worldwide about it and by using AdWords--but no sales. The site is http://www.ceramicdefects.com
The gurus say to expect failures. You have to keep trying new things and evaluating the performance by testing, testing, testing. Traffic is a problem. I have successfully sold money-making-books by advertising my web site (http://www.money-making-books.com) in national magazines. However, the profit margin was too low to warrant my continued efforts. You need to write your own books or ebooks to make it big!
Well, I've got to get out of here. I've got some more testing to do.
The End
John T. Jones, Ph.D. (tjbooks@hotmail.com), a retired college professor and business executive, Former editor of an international engineering magazine. To learn more about Wealthy Affiliate University go to his info site. If you desire a flagpole to Fly Old Glory, go to the business site.
More info: http://www.InternetBusinessToolCenter.com
Posted by
1
comments (0)
It is common that people receive friend requests from anonymous email addresses. There are many who even accept these kinds of requests but this may lead to some serious consequences in future. Users who send you those anonymous emails may hack into your system or may even steal your financial data. There are many occurrences of these incidents reported these days.
Considering the security involved in these kinds of problems, it is not a bad idea to do email address search on the anonymous email id before you decide to reply on those requests or add to your contact list. This process of searching the details of a person using email address is called reverse email address search. This type of email addresses search was not always possible for the common internet users as it was used only by law enforcement and investigation agencies.
But now many websites are providing the reverse email search method for free and anyone can use it. The process of doing email addresses search becomes difficult if the user you are searching for is not a registered one with these websites. To increase your chance of finding the person's details you can get the IP address of that person from the email he sent you and then enter that IP address in the email address search for a very specific result.
The only thing you must consider about email address search websites is to make sure that whether they are free or they require some membership. If the website required membership then you can search for some other free email id search website from Google or some other good search engine.
Considering the security involved in these kinds of problems, it is not a bad idea to do email address search on the anonymous email id before you decide to reply on those requests or add to your contact list. This process of searching the details of a person using email address is called reverse email address search. This type of email addresses search was not always possible for the common internet users as it was used only by law enforcement and investigation agencies.
But now many websites are providing the reverse email search method for free and anyone can use it. The process of doing email addresses search becomes difficult if the user you are searching for is not a registered one with these websites. To increase your chance of finding the person's details you can get the IP address of that person from the email he sent you and then enter that IP address in the email address search for a very specific result.
The only thing you must consider about email address search websites is to make sure that whether they are free or they require some membership. If the website required membership then you can search for some other free email id search website from Google or some other good search engine.
Posted by
1
comments (0)
If you are a MMORPG (Massively Multiplayer Online Role Playing Game) player, then you are probably a World of Warcraft addict. If you are then you know all about the frustrations and difficulties when trying to get ahead in the World of Warcraft. Running around like a pauper with no sense of direction and no idea which way to go and worst of all your gold pouch is always empty.Gaming online is supposed to be fun, isn't it? Well I don't know about you but spending hours doing boring and tedious tasks like farming,cooking,blacksmithing,skinning or worst of all repeating old quests that you have all ready completed twenty or more times just so you can make a little gold so you can try to advance your character just a little way.
We have all looked around the internet for a little help when it comes to playing World of Warcraft. But beware of a lot of the so called World of Warcraft help out there. Unfortunately there are plenty of bad people who wouldn't think twice about selling you useless out of date information or even information that could get your account banned from World of Warcraft. Yes you heard that right, your World of Warcraft account could be shut down temporarily or even permanently. Blizzard Entertainment has strict rules and regulations regarding proper manners and fair game play in World of Warcraft. Failure to comply with these rules or the use of cheats or hacks is strictly forbidden and will cause your account to be suspended or possibly even banned.
What a horrible feeling it would be to all of a sudden, not be able to play your favorite character in your favorite game with your good friend's. Make sure this doesn't happen to you. Be careful of emails disguised to look like they came from World of Warcraft or Blizzard Entertainment that ask for your personal World of Warcraft account information. If you ever receive one go straight to World of Warcraft help to learn if it is legitimate or a fraud. Ask World of Warcraft help to look at the email if need be. It's just not worth the risk. There are so many scam's out there that I could never name them all. If you see anything that offers to sell you gold or items, or says that they are going to give you something of value in return for something simply say no thanks and be on your way. Anyone that even mentions swapping accounts, free accounts, free account upgrades or improvements to your account or character that sound like innocent gestures are probably not, so stay clear of them. Make sure to read up on what is acceptable and not acceptable in World of Warcraft. Don't let someone else ruin your good reputation.
If you are looking for some help on how to play World of Warcraft better without cheats or hacks go to a safe World of Warcraft training site that is carefully monitored and regularly updated and built upon. There you will find an abundance of great World of Warcraft playing information that will not put your World of Warcraft account in jeopardy. Not only will you find general World of Warcraft playing help like gold getting, but even Horde or Alliance specific, character class specific and even profession specific help. So start enjoying World of Warcraft even more by learning to play it safely and more effectively.
We have all looked around the internet for a little help when it comes to playing World of Warcraft. But beware of a lot of the so called World of Warcraft help out there. Unfortunately there are plenty of bad people who wouldn't think twice about selling you useless out of date information or even information that could get your account banned from World of Warcraft. Yes you heard that right, your World of Warcraft account could be shut down temporarily or even permanently. Blizzard Entertainment has strict rules and regulations regarding proper manners and fair game play in World of Warcraft. Failure to comply with these rules or the use of cheats or hacks is strictly forbidden and will cause your account to be suspended or possibly even banned.
What a horrible feeling it would be to all of a sudden, not be able to play your favorite character in your favorite game with your good friend's. Make sure this doesn't happen to you. Be careful of emails disguised to look like they came from World of Warcraft or Blizzard Entertainment that ask for your personal World of Warcraft account information. If you ever receive one go straight to World of Warcraft help to learn if it is legitimate or a fraud. Ask World of Warcraft help to look at the email if need be. It's just not worth the risk. There are so many scam's out there that I could never name them all. If you see anything that offers to sell you gold or items, or says that they are going to give you something of value in return for something simply say no thanks and be on your way. Anyone that even mentions swapping accounts, free accounts, free account upgrades or improvements to your account or character that sound like innocent gestures are probably not, so stay clear of them. Make sure to read up on what is acceptable and not acceptable in World of Warcraft. Don't let someone else ruin your good reputation.
If you are looking for some help on how to play World of Warcraft better without cheats or hacks go to a safe World of Warcraft training site that is carefully monitored and regularly updated and built upon. There you will find an abundance of great World of Warcraft playing information that will not put your World of Warcraft account in jeopardy. Not only will you find general World of Warcraft playing help like gold getting, but even Horde or Alliance specific, character class specific and even profession specific help. So start enjoying World of Warcraft even more by learning to play it safely and more effectively.
Posted by
1
comments (0)
Everybody knows about hacking and its threat to Internet users, but the question is, would anyone even know that he's been hacked? The answer is no. When an individual hijacks a computer, the trick is to do so without letting the owner know. Otherwise, emergency safety software and other measures will be used, thus, making hacking no longer possible at that particular time. The trick is, therefore, to hack secretly so the hacking can continue for an amount of time significant to the hacker as he advances his selfish ends.
What makes things worse is the fact that many homes and business these days have opened up to wireless technology for convenience. Most of them do not know that this also makes it very convenient for cyber criminals to hatch their evil plots. With these wireless networks, hackers can simply be a few feet away and be able to enter the network and bully every computer in it. In fact, this type of hacking is now so rampant that one can find public sites selling known open wireless networks for hackers to target next.
Once a computer has been hacked, it will be known as a "zombie." A zombie computer would now be serving the hacker in a number of ways from sending spam emails to contaminating other computers with viruses. Some owners are even unaware that their computers have been used to spread pornographic materials or hack government systems. By this time, the computer is fully available to the hacker for control. Hackers even protect themselves from each other by healing security holes in zombie computers so that no other hacker can break in.
These days, the number of zombie computers is pegged at 450,000 around the world which are used for the lone purpose of sending spam email. Presumably, more of these zombies are being utilized for other cyber crimes such as identity thefts and unauthorized credit card use.
These days, it's impossible to thrive online without putting up a good fight against these hackers. However, since the IP address is the only thing that links a hacker to his victim, hiding this IP address should solve the problem of hacking. Why? Because without a computer's real IP, a hacker cannot trace that computer. Thus, no hacking of that computer can happen.
Get an IP changing software and discover how it feels to surf safely simply by hiding your IP address.
What makes things worse is the fact that many homes and business these days have opened up to wireless technology for convenience. Most of them do not know that this also makes it very convenient for cyber criminals to hatch their evil plots. With these wireless networks, hackers can simply be a few feet away and be able to enter the network and bully every computer in it. In fact, this type of hacking is now so rampant that one can find public sites selling known open wireless networks for hackers to target next.
Once a computer has been hacked, it will be known as a "zombie." A zombie computer would now be serving the hacker in a number of ways from sending spam emails to contaminating other computers with viruses. Some owners are even unaware that their computers have been used to spread pornographic materials or hack government systems. By this time, the computer is fully available to the hacker for control. Hackers even protect themselves from each other by healing security holes in zombie computers so that no other hacker can break in.
These days, the number of zombie computers is pegged at 450,000 around the world which are used for the lone purpose of sending spam email. Presumably, more of these zombies are being utilized for other cyber crimes such as identity thefts and unauthorized credit card use.
These days, it's impossible to thrive online without putting up a good fight against these hackers. However, since the IP address is the only thing that links a hacker to his victim, hiding this IP address should solve the problem of hacking. Why? Because without a computer's real IP, a hacker cannot trace that computer. Thus, no hacking of that computer can happen.
Get an IP changing software and discover how it feels to surf safely simply by hiding your IP address.
Posted by
1
comments (0)
iPhone hacks are applications developed to make it possible for you to make your iPhone perform like a mobile Smartphone. With the iPhone hacks, you can let loose all the concealed features, invent applications for your iPhone and iPod and unleash the devices to control the network utilities and game emulators. All in all, with these hacks, you can do almost anything with your mobile.
You will be able to import whole movie collections and save them from You Tube videos, access your home network and control your desktop, check your email and receive MMS messages, run any desired application on your phone's background, incorporate the iPhone with the car stereo and built electronic bridges for yourself, which can be connected to keyboards.
We have been made to believe that what iPhones have to offer is adequately sufficient but there is a lot more to be gained from them through the hidden features. The producers of the iPhone may be against this discovery and will therefore try to hinder you from using these features. Therefore, you will need the iPhone hacks to perform some of these tasks on your iPhone. With them, your iPhone will become full functional, enhancing your mobile experience.
The first hack is on getting push Gmail on the iPhone. The latest iPhones have the push options but they leave out a Gmail push version. However, in the absence of this version, you can use the prowl application. While the uses fetch to collect your emails, push will get the emails at the actual time. This saves your battery as the emails are directly forwarded to the server.
To get push Gmail, you use the Prowl- Growl application store, which allows the iPhone to get connected to Growl, a simple program whose main function is to notify you. It gives alerts on whatever you order it to. Therefore with Growl, you are notified whenever you have a new email. You just have to set it up so that it notifies you whenever there are new emails on your Gmail.
The second hack is on how to permit tethering. You do this by first installing iPhone 3.0, and then visit a specific site through the safari browser on the iPhone. The process is quite short and it allows easy tethering. However, be warned of charges from AT&T and this should be done at your own risk. Apple does not allow you to sync the iPhone with several iTunes libraries at a time. Therefore you can only sync up with one library at a time. Once you try going against this you risk erasing whatever is in the iPhone. To trick iTunes, you just have to change the "Library Persistent ID".
There is also a way out in moving apps between pages quickly. This is one of the biggest pains for average iPhone users. Most of them do not realize that ALL apps can be moved. There is another method as opposed to dragging them to the side of every individual page. All you have to do is place it at the silver dock. Once you have done this, scroll up to the last page, and then drag it in. There are many more hacks to help you make your iPhone fully functional to find out more, visit our sites to learn more on the iPhone tricks.
You will be able to import whole movie collections and save them from You Tube videos, access your home network and control your desktop, check your email and receive MMS messages, run any desired application on your phone's background, incorporate the iPhone with the car stereo and built electronic bridges for yourself, which can be connected to keyboards.
We have been made to believe that what iPhones have to offer is adequately sufficient but there is a lot more to be gained from them through the hidden features. The producers of the iPhone may be against this discovery and will therefore try to hinder you from using these features. Therefore, you will need the iPhone hacks to perform some of these tasks on your iPhone. With them, your iPhone will become full functional, enhancing your mobile experience.
The first hack is on getting push Gmail on the iPhone. The latest iPhones have the push options but they leave out a Gmail push version. However, in the absence of this version, you can use the prowl application. While the uses fetch to collect your emails, push will get the emails at the actual time. This saves your battery as the emails are directly forwarded to the server.
To get push Gmail, you use the Prowl- Growl application store, which allows the iPhone to get connected to Growl, a simple program whose main function is to notify you. It gives alerts on whatever you order it to. Therefore with Growl, you are notified whenever you have a new email. You just have to set it up so that it notifies you whenever there are new emails on your Gmail.
The second hack is on how to permit tethering. You do this by first installing iPhone 3.0, and then visit a specific site through the safari browser on the iPhone. The process is quite short and it allows easy tethering. However, be warned of charges from AT&T and this should be done at your own risk. Apple does not allow you to sync the iPhone with several iTunes libraries at a time. Therefore you can only sync up with one library at a time. Once you try going against this you risk erasing whatever is in the iPhone. To trick iTunes, you just have to change the "Library Persistent ID".
There is also a way out in moving apps between pages quickly. This is one of the biggest pains for average iPhone users. Most of them do not realize that ALL apps can be moved. There is another method as opposed to dragging them to the side of every individual page. All you have to do is place it at the silver dock. Once you have done this, scroll up to the last page, and then drag it in. There are many more hacks to help you make your iPhone fully functional to find out more, visit our sites to learn more on the iPhone tricks.
Posted by
1
comments (0)
This is a story about how my PayPal account got hacked and how I got it back. I had an unlucky day but with a little tinge of lady luck's blessings which helped me to get back to square one. This story gives a good advice for all the PayPal account holders on earth.
Day 1 - 8.30 PM IST
I just logged in into my gmail account to check the emails, I was shocked to see 4 emails from PayPal. 1. Password Changed, 2. Payment sent to some email address 3. Bank accounts removed 4. Primary email address changed. Oh my God!, I had $X,XXX in PayPal balance. While I was seeing these emails my gmail also got logged out. When I tried to login again, it did not. The hacker watched my every move. My primary email ID was the one which I used for all my business and personal contacts and it had 14000 archived emails and chat conversations.
I was feeling like blindfolded and left in a unknown forest. I just could not believe that this had happened to me. I had Norton anti virus + norton internet security and Spyware doctor, both of them licensed versions!! I know all about fake emails and phishing stuffs, I never clicked on suspicious links.
I realized that... "You are safe only if no one targets to attack you."
After a few minutes, someone added me to Yahoo messenger and said 'Hi'. I guessed that it was the hacker and it was. The very first sentence he told me was 'Hi, don't worry, you will get back everything within 7 days' .. He told me that he was a good guy and this is the first time he hacked someone. He also told me that he was in real need of the funds and would return my funds within 7 days. I almost believed him. I told him to give back my gmail account and told him that it was very important to me, and to my surprise he gave it back. He asked me what password I needed for the new account and he set it. I logged in and changed the password again. I was happy that I got back my gmail but was still very uncomfortable about the feeling that someone had watched me for so long!!
I was late in the night, I was sleepy but I had to hold on. I backed up all my files in my iPod and did a system recovery. After 45 minutes, my PC was as good as new. I again changed all the passwords and got back to sleep at midnight.
Day 2 - 6.00 AM IST
I saw my friend was online. I chatted with him and told him the entire story. He scolded me that I have not responded in timely fashion. He was so sure that the hacker was no good and chatted with me to make sure I don't call PayPal. The hacker did not achieve that but however he delayed me by 10 hours. I spent nearly 30 minutes waiting for PayPal representative and then some one showed up. I told PayPal, the entire story and they listened carefully. They assured me that 'I will not be held responsible for unauthorized payments sent from my account'. I felt good but not very good, I was not so sure that I would get back the money. I did what I could have done and I needed to relax. I took rest from this issue.
Day 3 - 7 PM EST
I called PayPal again. It needs a ton of patience to get connected with them. It took a few minutes to spot my account. They told me that "Your fraudulent payments were reversed, did you check your account". I just jumped right there and was so happy. But I COULD NOT LOGIN into my PayPal because the password was not with me! :(
I was not able to reset my password because the hacker also changed the security questions! They advised me to send all the documents and they will help to recover the password.
After a few minutes the hacker came online again. And LOL what nerves he got!!.. He asked me to send the documents to him because he said my account got limited and needs to be unlocked!! I refrained myself from talking abusive words and just managed the situation and logged out.
Day 4 - 6 PM EST
I logged in into yahoo messenger and I saw that the hacker had left me an offline message. Wow! he got frustrated I guess. He left me the PayPal email and password. I logged in and viola! I went inside my PP. Lovely moment it was.. The balance was intact. The four fraudulent payments were reversed. The account was limited though. I just printed the fax cover sheet and sent them the docs.
Day 4 - 3 PM IST
I got an email that my PayPal account has been restored. I immediately went in and sent 4 big payments to my friends and family members. I could breathe now again!
Now whats next?.. everything is back to square one! Now that I have learnt a good lesson. If we think something like "This can never happen to me" you actually attract that situation and within a few days you realize it... the dream comes true.. even though its a bad dream in this case.
I contacted me friends and everyone told me that I need to kick out Norton and Spyware Doctor and buy Kaspersky because thats what is best in the market. I went to that site and reviewed their products. They had anti virus and Internet Security 7.0. The anti virus comes inbuilt within Internet Security and hence its enough to buy the latter one. For one year it costs around $60 and for 2 years its around $95. I just bought it right away and installed it, activated it. Again I changed all my important passwords.
Bottom line: If you think it wont happen to you, one day it will happen, and you will think about the day when you thought that it won't happen to you.
Now that I got my money back, but it may not happen all the time to all the people. You just need to be on top of it.
Day 1 - 8.30 PM IST
I just logged in into my gmail account to check the emails, I was shocked to see 4 emails from PayPal. 1. Password Changed, 2. Payment sent to some email address 3. Bank accounts removed 4. Primary email address changed. Oh my God!, I had $X,XXX in PayPal balance. While I was seeing these emails my gmail also got logged out. When I tried to login again, it did not. The hacker watched my every move. My primary email ID was the one which I used for all my business and personal contacts and it had 14000 archived emails and chat conversations.
I was feeling like blindfolded and left in a unknown forest. I just could not believe that this had happened to me. I had Norton anti virus + norton internet security and Spyware doctor, both of them licensed versions!! I know all about fake emails and phishing stuffs, I never clicked on suspicious links.
I realized that... "You are safe only if no one targets to attack you."
After a few minutes, someone added me to Yahoo messenger and said 'Hi'. I guessed that it was the hacker and it was. The very first sentence he told me was 'Hi, don't worry, you will get back everything within 7 days' .. He told me that he was a good guy and this is the first time he hacked someone. He also told me that he was in real need of the funds and would return my funds within 7 days. I almost believed him. I told him to give back my gmail account and told him that it was very important to me, and to my surprise he gave it back. He asked me what password I needed for the new account and he set it. I logged in and changed the password again. I was happy that I got back my gmail but was still very uncomfortable about the feeling that someone had watched me for so long!!
I was late in the night, I was sleepy but I had to hold on. I backed up all my files in my iPod and did a system recovery. After 45 minutes, my PC was as good as new. I again changed all the passwords and got back to sleep at midnight.
Day 2 - 6.00 AM IST
I saw my friend was online. I chatted with him and told him the entire story. He scolded me that I have not responded in timely fashion. He was so sure that the hacker was no good and chatted with me to make sure I don't call PayPal. The hacker did not achieve that but however he delayed me by 10 hours. I spent nearly 30 minutes waiting for PayPal representative and then some one showed up. I told PayPal, the entire story and they listened carefully. They assured me that 'I will not be held responsible for unauthorized payments sent from my account'. I felt good but not very good, I was not so sure that I would get back the money. I did what I could have done and I needed to relax. I took rest from this issue.
Day 3 - 7 PM EST
I called PayPal again. It needs a ton of patience to get connected with them. It took a few minutes to spot my account. They told me that "Your fraudulent payments were reversed, did you check your account". I just jumped right there and was so happy. But I COULD NOT LOGIN into my PayPal because the password was not with me! :(
I was not able to reset my password because the hacker also changed the security questions! They advised me to send all the documents and they will help to recover the password.
After a few minutes the hacker came online again. And LOL what nerves he got!!.. He asked me to send the documents to him because he said my account got limited and needs to be unlocked!! I refrained myself from talking abusive words and just managed the situation and logged out.
Day 4 - 6 PM EST
I logged in into yahoo messenger and I saw that the hacker had left me an offline message. Wow! he got frustrated I guess. He left me the PayPal email and password. I logged in and viola! I went inside my PP. Lovely moment it was.. The balance was intact. The four fraudulent payments were reversed. The account was limited though. I just printed the fax cover sheet and sent them the docs.
Day 4 - 3 PM IST
I got an email that my PayPal account has been restored. I immediately went in and sent 4 big payments to my friends and family members. I could breathe now again!
Now whats next?.. everything is back to square one! Now that I have learnt a good lesson. If we think something like "This can never happen to me" you actually attract that situation and within a few days you realize it... the dream comes true.. even though its a bad dream in this case.
I contacted me friends and everyone told me that I need to kick out Norton and Spyware Doctor and buy Kaspersky because thats what is best in the market. I went to that site and reviewed their products. They had anti virus and Internet Security 7.0. The anti virus comes inbuilt within Internet Security and hence its enough to buy the latter one. For one year it costs around $60 and for 2 years its around $95. I just bought it right away and installed it, activated it. Again I changed all my important passwords.
Bottom line: If you think it wont happen to you, one day it will happen, and you will think about the day when you thought that it won't happen to you.
Now that I got my money back, but it may not happen all the time to all the people. You just need to be on top of it.
Posted by
1
comments (0)
With IT equipment and computers so widely used in modern day business, the opportunity for criminal activity to take place increases. As a result of this, more and more companies are looking for help from computer forensics specialists. Computer investigations require a high level of expertise to identify if misuse has taken place and to what extent. One of the most harmful forms of criminal computer activity is hacking, which unfortunately is not just the preserve of movies anymore. Identifying and preventing hacking is essential to safeguarding any business's operations, regardless of size.
Computer forensics can investigate instances where an individual or organisation believes their systems have been the victim of misuse. Specialists will be able to investigate a variety of misuse methods - including hacking attacks - and extract the necessary evidence in order to act in legal proceedings. We can also provide guidance to help prevent future attacks.
Computer hacking is usually undertaken by career criminals who wish to steal personal information and access sensitive company information, using highly sophisticated and difficult to trace techniques. Identifying this is central to a prosecution, which is why we are happy to act as an expert witness in court. We can often present complex and highly technical issues that go into forming a forensic examination and present these in a manner that all parties can understand.
Forensic providers draw on an array of investigative techniques for discovering data present in a computer system, and in the recovery of deleted or relevant files. This is essential to the presentation of evidence in court cases and in employment tribunals. These investigations can not only uncover evidence of hacking, but the theft of intellectual property, electronic fraud, the accessing of inappropriate or illegal websites etc.
A court proceeding can live or die by the quality of the information provided by expert witnesses. The key to providing an effective witness service is the comprehensive training given to those who appear in court. Analysts at digital forensics companies should have undergone thorough tuition that covers the broad spectrum of cross-examination and courtroom presentation. In short, they can ensure that your computer forensics and digital misuse investigations are carried out to the highest standard.
Computer forensics can investigate instances where an individual or organisation believes their systems have been the victim of misuse. Specialists will be able to investigate a variety of misuse methods - including hacking attacks - and extract the necessary evidence in order to act in legal proceedings. We can also provide guidance to help prevent future attacks.
Computer hacking is usually undertaken by career criminals who wish to steal personal information and access sensitive company information, using highly sophisticated and difficult to trace techniques. Identifying this is central to a prosecution, which is why we are happy to act as an expert witness in court. We can often present complex and highly technical issues that go into forming a forensic examination and present these in a manner that all parties can understand.
Forensic providers draw on an array of investigative techniques for discovering data present in a computer system, and in the recovery of deleted or relevant files. This is essential to the presentation of evidence in court cases and in employment tribunals. These investigations can not only uncover evidence of hacking, but the theft of intellectual property, electronic fraud, the accessing of inappropriate or illegal websites etc.
A court proceeding can live or die by the quality of the information provided by expert witnesses. The key to providing an effective witness service is the comprehensive training given to those who appear in court. Analysts at digital forensics companies should have undergone thorough tuition that covers the broad spectrum of cross-examination and courtroom presentation. In short, they can ensure that your computer forensics and digital misuse investigations are carried out to the highest standard.
Posted by
1
comments (0)
How to Hack Facebook Account Passwords Using Trojans & Keyloggers
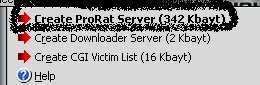
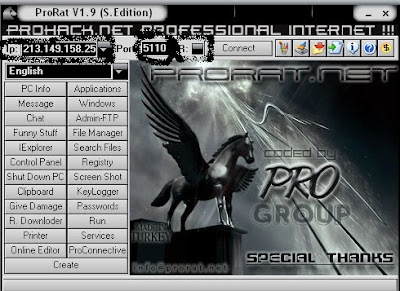
STEP-2: Creating the ProRat server. Click on the "Create" button in the bottom. Choose "Create ProRat Server".
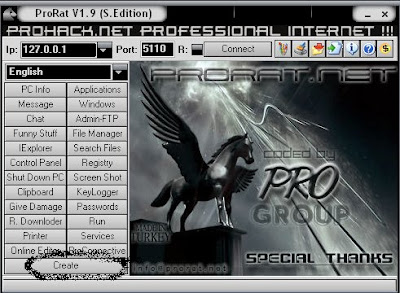 Here I am demonstrating using PRORAT trojan. You can also check the list of trojans & Keyloggers here which I have already posted few months back. You can use any trojan or keylogger as per your ease. The basic functionality of all backdoors are same. Pls make note that all these hacking tools and softwares are detected by antivirus. You have to uninstall or close you running antivirus first. I strictly recommend you to try these trojans & keyloggerson some testing system first.
Here I am demonstrating using PRORAT trojan. You can also check the list of trojans & Keyloggers here which I have already posted few months back. You can use any trojan or keylogger as per your ease. The basic functionality of all backdoors are same. Pls make note that all these hacking tools and softwares are detected by antivirus. You have to uninstall or close you running antivirus first. I strictly recommend you to try these trojans & keyloggerson some testing system first.Step-1: Download latest version of ProRat v1.9 Fix2. CLICK HERE to download. The ZipPass is : pro
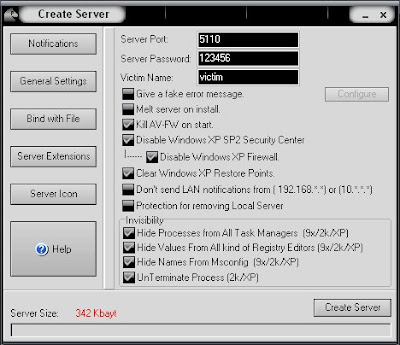
STEP-3: Open Notifications. Select second option "Mail Notification". In the E-MAIL field you will see a mail
id: bomberman@yahoo.com. Remove this mail ID and give your own mail id here. You will receive a notification
email on this email id whenever you victim will be connected to internet from the infected system.
STEP-4: Open General settings. This tab is the most important tab. In the check boxes. here is a quick overview
of what they mean and which should be checked.
Key:
[ ] = dont check
[x] = check
[ ] Give a Fake Error Message. (when they open the file, it gives an error message.
[x] Melt server on install. (this will cause the server to ALWAYS connect to the internet when the victim gets
online)
[x] Kill AV - FW on Install. (this causes the anti-virus and firewalls to SHUT DOWN and stay off once installed
on the victim's computer.
[x] Disable Windows XP SP2 security center
[x] Disable Windows XP Firewall
[x] Clear Windows XP Restore Points
[ ] Dont send LAN notifications ( keeps other computers on the victim's network from knowing about you )
[ ] Protection for removing local server
In the Invisibility Box, check all 4 boxes.
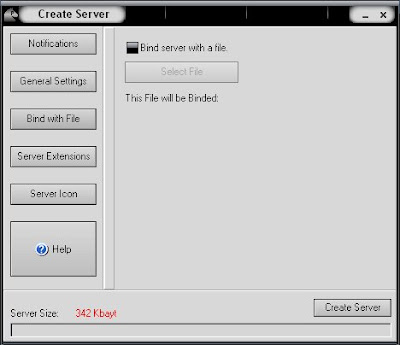
STEP-5: Open Bind With File. You can bind your server\downloader server with a file that you want. You must
click on the ''Bind the server with a file'' button and then the file button will be activated. You can choose
a file to be binded with the server now. A good suggestion is a picture because that is a small file and its
easer to send to the people you need.
STEP-6: Open Server Extensions. I prefer using .exe files, because it is cryptable. Mostly crypters don't
support .bat/.pif/.com etc. So use .exe files.
STEP-7: Open Server Icon. You can select the one you want to use with the server from the small pictures on the
menu. You can use an icon from your computer also. Press the "Choose new icon" button.
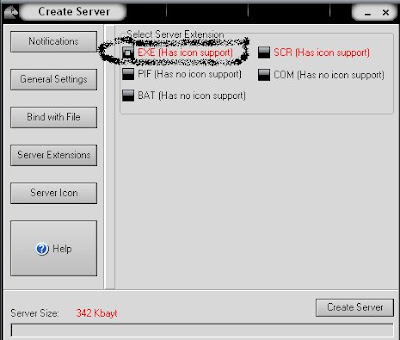

STEP-8: After this, press "Create server", your server will be in the same folder as ProRat. A new file with
name "binded_server" will be created. Rename this file to something describing the picture.
[NOTE: PLS DO NOT OPEN THE FILE "binded_server" on your system.]
STEP-9: Sending this file "binded_server" to victim. You can send this trojan server via email, pendrive or if
you have physical access to the system, go and run the file.
and then email it. Once your victime download this ZIP file, ask him to unlock it using ZIP password. When From EMAIL, you can not send this file as it is because it will be detected as TROJAN OR VIRUS.
the victim will double click on the file, he will be in your control.
STEP-10: Connecting to the victim's computer. Once the server has been sent and the person has opened this ZIP
folder, they will now be infected with it. AND HAVE NO CLUE ABOUT IT!. On the top of the ProRat program you
will see a box in the upper left corner. Type in the victim's IP address and make sure the port is 5110. Now
press Connect. You should now see a pop-up box wanting to know a password. Remember the password you entered
while creating the server? that is what you need to type. By default, it is "123456" without quotes.
STEP-11: Check your email, (junk in needed), and find the “Your victim is online”. Copy and paste the IP
address onto ProRat where it says “IP:[127.0.0.1]“. Press CONNECT, DO NOT CHANGE THE PORT, if u did change it
back to 5110. Type in the password (default is usually 123456, it is in the email). Your done, now you can mess
with the buttons on the program. Especially the GIVE DAMAGE button. It will damage their pc by format, and will
make the computer useless.
Download latest version of ProRat v1.9 Fix2. to download. The ZipPass is : pro
FAQ:
Q: Error message:Windows cannot access the specified deice, path, or file. You may not have the appropriate
permissions to access the item. What do I do?
A: Simple! Delete the ProRat program. Delete it. What happen was, your AV has altered the file. OR it could be m
alacious content. Either way, delete it. NEXT, remember the file you downladed? Un extract the file again and
re run. You will not need to remake a server file and such if it has been sent to the victim. Just open ProRat
and make sure your AV is shut off. Reconnect. There ya go.
Q: What operating systems are supported by ProRat?
A: Windows 95/95B
Windows 98/98SE
Windows ME
Windows NT 4.0
Windows 2000
Windows XP
Windows Vista
Q: When I have downloaded ProRat, my antivirus detect it as virus. What should I do?
A: Well, since RATs are hacktools, and all the hack tools are detected as viruses, ProRat is detected as virus
also. To download and install ProRat you will need to
Posted by
1
comments (0)

Award Keylogger is fast, invisible and easy-to-use surveillance tool that allows you to find out what other users do on your computer in your absence. It records every keystroke to a log file.
The log file can be sent secretly with email or FTP to a specified receiver. Award Keylogger can also detection specified keywords and take a screenshot whenever one is typed, displaying findings in a tidy log viewer. It causes no suspicious slowdowns and takes very few system resources. all this is happening in full stealth mode so the person you are monitoring will never be aware of it.
Info: http://www.award-soft.com

Ardamax Keylogger v2.9 [With Working Serial Included]
Ardamax Keylogger is a useful keylogger that will record users activity and will save it to a logfile. It's very easy to use.
The logfile can be viewed as a text or web page. Use this tool to find out what is happening on your computer while your away, maintain a backup of your typed data automatically or use it to monitor your kids.
Download:-http://hotfile.com/dl/39718059/0799064/ak30_knight999.rar.html
Posted by
1
comments (0)

Free Keylogger monitors computer activities.
Freeware Keylogger is a completely free award winning monitoring application. It runs in the background and allows you to monitor all keyboard activities performed on your PC, visited websites, e-mail, chat, openned application and files. Freeware Keylogger helps you to find out, what exactly took place in the system. You will find out what your employee or children search in the internet, and to check them. You will be able to view the reports as HTML files. The software is 100% Free application.
product submission by Company Rep
Download:-http://www.ultimatekeylogger.com/downloads/freewarekeylogger.exe
| fact sheet |
| ID#: | 1271522016 |
| date posted: | May 3, 2010 |
| category: | Security:Filtering/Monitoring |
| platform: | WinXP,WinVista,WinVista x64,Win7 x32,Win7 x64,Win2000,Windows2000,Windows2003,WinServer,Windows Vista Ultimate x64,Win98,WinME,WinNT 3.x,WinNT 4.x,Windows Vista Home Premium |
| vendor: | KRyLack |
Posted by
1
comments (1)

Here is the last version release of DarkComet Remote Administration Tool
DarkComet-RAT (Remote Administration Tool) is a fast/powerfull and stable remote admin tool that alloud you to control the whole remote computer , you can view the desktop / webcam / manage process / listen to the sound etc… in the same time with a realy good speed , DarkComet is work in localhost , LAN ( Local Area Network ) , and WAN ( Wide Area Network ) .
He is compatible with [Windows 2000 , Windows XP (all sp), Windows Vista (all sp) and Windows Seven] For 32(.386) and 64 bit machines.
To use it on VMWare you must choose the bridge option for network , ( NAT mode ) seems to lost some packets on transfers about 90% of the functions of DarkComet.
The Client is full Coded in Pascal/Delphi using CodeGear Delphi RAD 2010 ( UNICODE ).
The Server is coded in Pascal/Delphi ans Inline Assembler code using Delphi 2007 ( ANSI ).
Don’t forget to read disclaimer and EULA terms , when you choose to download this software you are fully responsable of the possible harmfull things you can do with it.
This software can be detect as a Virus/Backdoor/Trojan cause it alloud you to remote control a computer without any autorisation.
Download:-http://darkcomet-rat.com/download.php?id=2
Posted by
1
comments (0)
Lost Door is a backdoor trojan horse family of more than 10 variants which can infect Windows operating systems from 95 to XP. It was created by OussamiO and built using Visual Basic. It uses the typical server, server builder, and client backdoor program configuration to allow a remote user, who uses client, to execute arbitrary code on the compromised machine (which runs the server whose behavior can be controlled by the server editor). The server component (75,053 bytes) when running, connects to a predefined IP address on TCP port 2185, awaiting commands from the remote user who uses the client component can execute arbitrary code at will on the compromised machine.

Features
Lost Door allows many malicious actions on the victim's machine. Some of its abilities include:
- Reverse connection
- Webcam shot
- Date and time manager
- printer
- Control panel
- PC control
- Executor
- Dos command
- Windows manager
- Screen shot
- Remote server manager
- Server remover
- Ip Grabber
- Server Downloader
- Icon Changer
- Audio Streaming
- Encrypt Settings
- Volume Control
- Connection Logs
- Installed Application
- Infect All USB
- Multilanguage
- Services Viewer
- Remote passwords
- MSN Controller
- Remote Shell
- Chat with server
- Send fake messages
- files manager
- Find files
- Change remote screen resolution
- Information about remote computer
- Clipboard manager
- Internet Explorer options
- Running Process
- Online key-logger
- Offline keylogger
- Fun Menu
Infection Method
Lost Door has a server creator with features that allow it to be undetected by antivirus and firewall software, and also allow it to stealthily run in the background. The software only runs completely (including rootkit) in Windows XP/2000. Such features include disabling security software, removing and disabling system restore points, and displaying a fake error message to mislead the victim.

This version is now detectable by ESET NOD32 Antivirus. For other AV's, I have not checked.
Server
Dropped Files:
c:\WINDOWS\system32\dlllhost.exe
Size: 129,808 bytes
Added to Registry:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run "Winupdate"
Data: C:\WINDOWS\system32\dlllhost.exe
REFERENCES
- http://www.checkpoint.com/defense/advisories/public/2009/cpai-30-Mar.html
- http://www.megasecurity.org/trojans/l/lostdoor/Lostdoor_all.html
- http://www.techmantras.com/content/lost-door-32-rat
Posted by
1
comments (0)
Download Free Hacking Tools: 33 Best Hacking Tools

Well, I've gained a lot of tools , so I decided it'd be a good idea to give some of it back to the community. I've made this pack which contains most of my hacking tools collection (though not all Non). There's 33 (or more) tools in here.
KEYLOGGERS & PASSWORD STEALING:
- Ardamax 2.8
- Ardamax 3.0
- Fake Messenger w/ password retriever (Revenge Messenger)
- Silent Keylogger by BUNNN
- Digital Keylogger v3.3
- Infinity YouTube cracker (doesn't work according to many but its still present)
CRYPTERS AND BINDERS:
- File Joiner v2.01
- File Injector v3
- Xeus Technologies HotFusion binder
- Japabrz's Csharp crypter
- Daemon Crypt V2
- Crypter v1.2
- nBinder v5.5 premium
- Easy Binder v2
- Shell Labs Icon Changer
- ShockLabs file binder
- uBinder v1.30 SE (someone's private binder, it is almost FUD)
FREEZERS & BOMBERS:
- Frozen Land MSN Freezer v1
- Facebook Freezer
- Hotmail Lockers
- Email Bomber (an HTML page, no exe required!)
RATS:
- Beast v2.07
- BitFrost v1.2
- Dark Moon v4.11
- Lost Door v2.2 Stable public edition
- MiniMo v0.7 public beta
- Nuclear RAT v2.1.0
- Optix v1.33
- PaiN RAT 0.1 beta 9
- Poison Ivy v2.3.2
- Shark 3
- Spy-Net v.1.7
- Y3 RAT v2.5 RC 10
OTHERS:
- Proxy Switch v3.9 Ultimate
- Savk AV Killers (all 5 safe and deadly versions)
- Ardamax keylogger remover
NOTE: All software is full and cracks/serials are included, there are no trials or demos.
SAFETY: It would be best to run all these tools either Sandboxed, or from a Virtual Machine.
Download:-http://hotfile.com/dl/45700645/e0e0a0e/33_HKPK_Tools.rar.html
Posted by
1
comments (0)
Centuno is now offering a Free Penetration Testing. Simulate an actual hacking attack with free Penetration Testing.

Classroom Spy Pro 3.4.4 | 11 MB
It is hard to teach a group of people how to use a PC, or even how to use a specific program on a PC or the internet. Yes, PC or web training isnt easy. For someone whos doing something right, there are probably two others doing it wrong, playing games, checking email, shopping
Classroom Spy lets you see what everyones doing - without leaving your desk. You can monitor the activity of all the PCs in your classroom remotely. Plus, you can share your screen with your students PCs, making demos and presentations much easier.
What is it useful for?
* For monitoring and recording your students activities on a remote computers
* For monitoring students in the classroom to achieve better discipline or, just to assist them when they are in trouble (by using the remote control feature).
* For administrating all computers just from one location - your computer.
* For presenting your screen to students.
* For locking students computers while they are waiting for further instructions or assignments.
* Helping your students by showing your desktop to them.
* Turning off, restarting, remote computers with one click.
What are the major benefits of using Classroom Spy Professional?
* Installation and use of the application is very easy since all of the functions can be accessed with a few mouse clicks.
* You have complete control over what remote users are doing.
* Unlike other similar applications, this application provides you with a live picture of the remote computer screens. The live screen (due to some optimizations) does not use a high bandwidth, but even when the lower network bandwidth is required the refresh interval can be enlarged using one mouse click.
* You can make the presentation by showing your live screen to students
* Application allows you to take over the remote computer by controlling its mouse and keyboard.
* The remote computers? screens are represented in the table with a customizable number of rows as thumbnails.
* Using this application, you can always see which user is actually logged on to the remote computer.
* Schedule remote computers desktop recording
* Execute several actions on all remote computers with on click
Features:
+ Displaying a live picture of a remote computer.
+ You can take control of a remote computer by controlling its mouse and keyboard.
+ More remote screens can be displayed in a table.
+ A remote screen can be zoomed to an actual size.
+ The name of the connected user is displayed.
+ Record remote computers screens.
+ Show your desktop to students
+ Power off, restart, hibernate, suspend remote computers
+ Log off desktop users
+ Lock workstation
+ Control screensaver
+ You can lock selected remote computers
+ You can display a message on selected remote computers.
+ When lower bandwidth is required, the refresh interval can be enlarged.
+ Automatic connection to a remote computer is optional.
+ Settings for the agent are encrypted and password protected.
+ Connection to a remote computer is password protected.
+ Access to monitoring the console is password protected. If more users use the same computer, different profiles and access passwords can be set.
+ More monitoring consoles can be connected to the same remote computer - you can monitor your students from different locations.
+ Agent can run as an NT service (for Windows NT, 2000, XP, 2003).
+ Agent can run as a process (Windows 95, 98, Me).
+ Application can optionally use encrypted communication.
+ Agent can be remotely installed.
Download:-http://www.filesonic.com/file/8911247/Classroom.Spy.Pro.3.4.4.rar
Posted by
1
comments (0)
Download Ultimate Crackers Kit | Best Hacker Toolbox
Hacker Toolbox consists of the latest hacking tools. A profusion of hacking, cracking, phreaking tools & files will familiarize you with how hackers break into your machine and steal your information. You can also learn hacking
Techniques from a good collection of source codes for virus and tools, instructional documentation, tutorials and much more. You can act like a master hacker to customize your own program with the editors and executable file tools.
Categories: Backdoor, Crack tool, Disassembler, DoS tool, Document, E-mail tool, Editor, Encryption & decryption tool, Executable file tool, Icq tool, Keylogger, MISC, Packet forging, Phreak tool, Scanner, Sniffer, Snoop tool, Source
code, Spoof, Virus.
Download:-http://hotfile.com/dl/46508869/8099d3d/Ultimate.Crackers.Kit.v3.2.rar.html
Posted by
1
comments (0)
Remote Keyloggers Free Download | Best Keylogger Pack
Keylogger Pack
Keyloggers log everything that users do on a computer including all keystrokes, chat conversations, applications, windows, websites, passwords, and emails.
Some even record screenshots.
Log the chats from the most known chat programs like ICQ, Miranda, Skype, Google Talk, MSN, AIM, AOL, Yahoo, or QIP.
Content:
Keyloggers:
007 Spy Software v3.873
Ardamax Keylogger v3.1
Award Keylogger v1.8
Elite Keylogger v1.0
FKWP v1.5
FUD Keylogger
Ghost Keylogger v3.80
Local Keylogger Pro v3.1
Perfect Keylogger v1.68.2
Radar Spy
SC Keylogger Pro v3.2
SpyBuddy v3.7.5
Spytech Keystroke Spy v1.10
System Keylogger v2.0
Use a Binder and Crypter to make your keylogger undetectable.
Binders are software used to bind or combine two or more files in one file under one name and extension. You can bind with an image, movie, song, or any file you like.
Binders:
A+ Binder
Multi File Binder
Simple Binder
Weekend Binder
Crypters:
mdCrypter
Scantime Crypter
Keyloggers log everything that users do on a computer including all keystrokes, chat conversations, applications, windows, websites, passwords, and emails.
Some even record screenshots.
Log the chats from the most known chat programs like ICQ, Miranda, Skype, Google Talk, MSN, AIM, AOL, Yahoo, or QIP.
Content:
Keyloggers:
007 Spy Software v3.873
Ardamax Keylogger v3.1
Award Keylogger v1.8
Elite Keylogger v1.0
FKWP v1.5
FUD Keylogger
Ghost Keylogger v3.80
Local Keylogger Pro v3.1
Perfect Keylogger v1.68.2
Radar Spy
SC Keylogger Pro v3.2
SpyBuddy v3.7.5
Spytech Keystroke Spy v1.10
System Keylogger v2.0
Use a Binder and Crypter to make your keylogger undetectable.
Binders are software used to bind or combine two or more files in one file under one name and extension. You can bind with an image, movie, song, or any file you like.
Binders:
A+ Binder
Multi File Binder
Simple Binder
Weekend Binder
Crypters:
mdCrypter
Scantime Crypter
Download:-
http://hotfile.com/dl/10940725/92a5d5c/Keyloggers.rar.html
